The dark web has moved on from selling drugs – the new hot item is data – in vast quantities. And this is why security is becoming the key point of engagement between channels and customers.
Cyber Security Author of The Dark Net and cyber-blogger for the Telegraph Jamie Bartlett gave an insight into the nature of the dark web at last week’s very successful Channel-Sec conference. In many ways, he said, it is just like the rest of the Internet – but with extra pitfalls for the unwary.
He showed how the Tor browser, originally designed by the US Navy as a way to hide IP addresses, is now used to do any sort of work where identities are not revealed. It takes a bit longer to access sites as it has to encrypt and then bounce between repeaters, but is certainly used a lot by journalists and others needing not to be traced, he said.
And it is clever – l with layered protection – and known as the onion because of its layers. “But any site you go to knows you are using a Tor browser, so knows what to expect. It is not illegal and it is used by five million people daily. It is a way into the dark web – and leads to between 5000 and 20, 000 sites which use the same ways of hiding their identity”.
So here we have a network of sites that are difficult to censor or remove. On them, there are materials for sale, unaffected by copyright, and a lot of services such as commercial hacking. There is also a lot of terrorist and extremist material. Sometimes it gets removed by the FBI and law enforcement agencies, but it is easily reloaded. And it has a respectable side: even Facebook has a dark net presence, as do many large media groups.
All addresses are randomly generated and have a .onion extension. The most infamous shopping sites deal in drugs – the Silk Road did more than $1bn of business in 2011 and 2013. And it is very similar to Amazon or eBay – just without any limits as to what is bought and sold. All use crypto currencies and there are hundreds if not thousands of vendors. In 2013 for example, the top selling item was fake £10 Tesco vouchers.
So It is a market – with all that means in competition and choice and where people look around for the best deal. “And it works – users give feedback and this encourages vendors to deal in a straightforward way. It is used by one in four drug users in the UK; forget encryption and technology – it is just a marketplace - there are special offers, buy-one get pne free and reviews,” he told a surprised audience.
“You will not find a more creative bunch than criminals – so innovation and changes to avoid detection are running apace. There is even a community of darkweb users and vendors and they agree on the use of third parties to hold funds for transactions. And they are good at tech for example, they have been running elements of blockchain for longer than anyone else. Scam sites are going on as well but don’t work in the long term,” he said.
The change in the last year has been that drugs are no longer the most important items being bought and sold on the dark web – it is now stolen information. There is almost no limit to the amount of stolen information- estimates are that there are 3-4 billion user names and password combinations, for example.
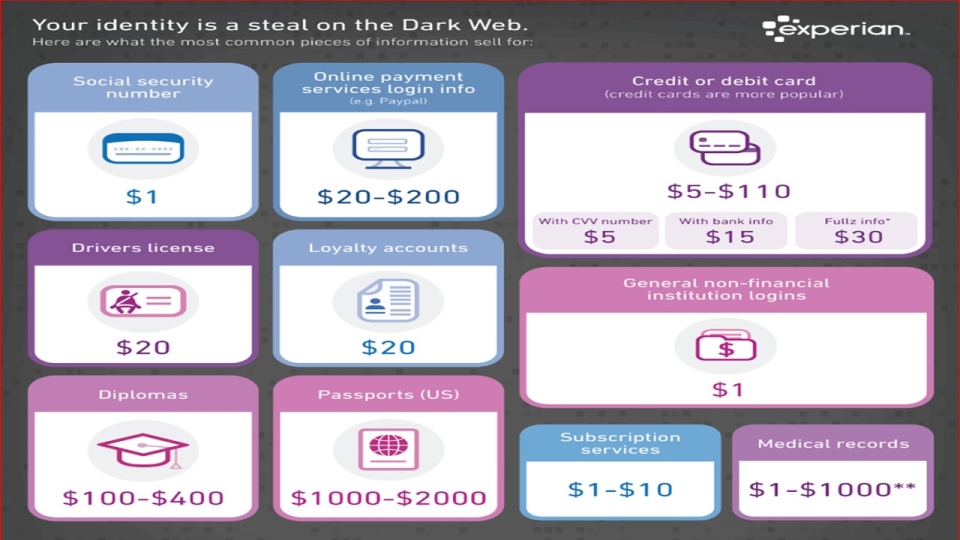
Any stolen data such as credit cards ends up on the dark web and goes on the market. Experian has discovered the typical buying prices [pictured]. In the EU the price is higher than in the US – because there are more cards across the Atlantic. “Dream Market” is the most popular of the big marketplaces and the volumes are vast – 50,000 offers of items for sale at present.
Then there are the services: Ransomware is a service that can be bought and sold. It is a low level form of cybercrime, and it relatively easy, the dark web even has guides on how to perform a credit card fraud, telling fraudsters what checks are in place. “Health records are available for identity theft , and it goes on and on, working in the same way as the Silk Road. With user reviews and product descriptions. The markets mean there is always demand and supply , constantly innovating and devising ways of working and making it easy for novices to get access to whatever.”
The higher-level dark web has more limited access and could be accessed on a protected forum offering data. Any software vulnerability will be being discussed, bought and sold in the protected forums. And it is smart: a few months ago, an FBI agent went onto a forum to check out a batch of stolen cards. But the people running the forum have a machine learning algorithm that uses a dataset of known FBI techniques. The model looks at what FBI agents tend to do and block them; so up comes a message calling out the FBI. The authorities are making progress, but the marketplace always seem to re-emerge, he warns.
Where this is all going is into a wider range of crypto currencies. Imagine working through layers of crypto currencies as well as encrypted links.
“What they [the bad guys] are trying to do now is make the markets work without servers- a dark net using blockchain and a distributed database. This is now being backed by investors in the legitimate part of the web, but the bad guys have got there first. It will be very difficult to shut down the criminals when it is all on blockchain. All of this creates a further vulnerability for internet enabled devices. IoT devices are already being listed on the dark web – it links to them and their data and connects to a database of vulnerabilities – it automatically hacks the devices, in fact. Crime is becoming automated.
And this is what is coming next.


